First published in the Daily Maverick 168 weekly newspaper.
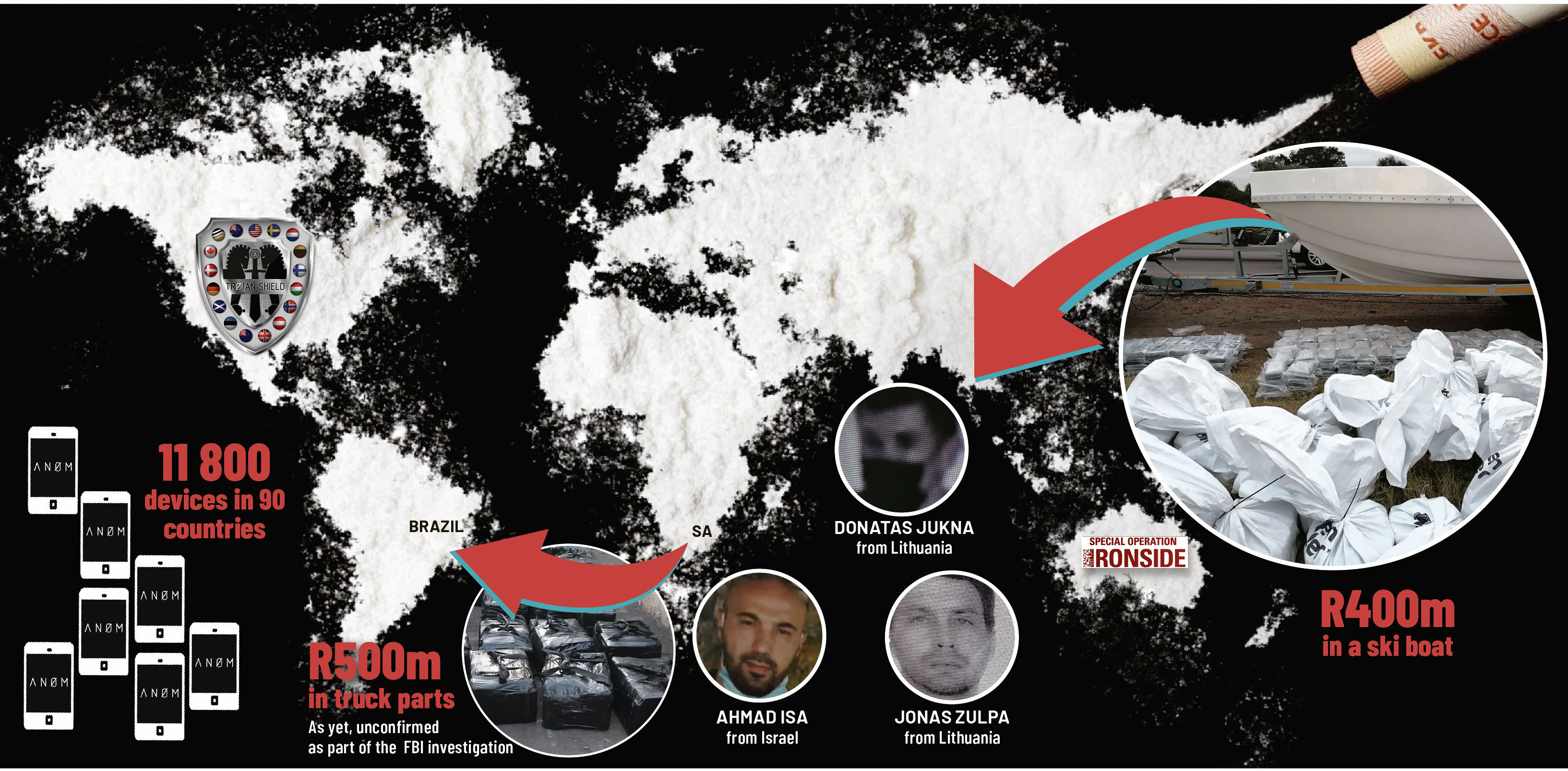
In less than three months, investigators in South Africa have made massive inroads into the global drug trade, intercepting more than R1-billion worth of cocaine (and seizing four tonnes of it since March), arresting several suspects and identifying international operatives in this country.
One of the recent crackdowns has resulted in a staggered series of arrests and suspects from other countries going on the run to evade detention in South Africa.
There are also possible ties to perlemoen smuggling, an international syndicate that previously trafficked drugs using, among various items, a Harry Potter book, and links to several countries including the US via its Operation Trojan Shield.
This operation involved encrypted communication devices sold via the black market to criminals who promoted these to each other – and which, unknown to them, the US’s FBI was lawfully bugging.
A map showing where these devices were used, contained in US documents, includes South Africa, and authorities here have acknowledged US and Australian investigations fed into a major cocaine bust in this country.
It is not the first time authorities have managed to infiltrate communication encryption services used by criminals worldwide, but these investigations stand out in terms of ingenuity and mark the first time the FBI ran its own encrypted device company.
In early June, the US said more than 500 arrests were carried out globally over 48 hours as a result of the novel investigation, which started a few years ago in San Diego. There were also more than 150 threats to life.
“This was an unprecedented operation in terms of its massive scale, innovative strategy and technological and investigative achievement,” the acting US attorney Randy Grossman said in a statement at the time.
“Hardened encrypted devices usually provide an impenetrable shield against law enforcement surveillance and detection. The supreme irony here is that the very devices that these criminals were using to hide from law enforcement were actually beacons for law enforcement.”
There have been massive drug crackdowns in SA since June this year, the same time at which the US said it had effectively been bugging criminals’ communication devices.
These include:
- On 2 June, R400-million worth of cocaine in a pure compressed form was discovered hidden in a ski boat being towed by a bakkie on the N1 in Pretoria. A suspect, Niel Pieter van Zyl, was arrested. A Hawks statement said: “The cocaine was reportedly destined for both the local and international markets organised by a drug syndicate operating in the country allegedly stockpiling a large quantity of cocaine in Gauteng.”
- On 6 June, a suspect from Lithuania, Tenikaitis Valdas, was arrested in connection with the ski-boat bust at OR Tambo International Airport while boarding a flight to Paris. The Hawks believe he may have been trying to flee SA.
- In mid-June three more suspects –Rafiq and Rasheed Baderoen, as well as Michael Norman – were detained in Cape Town over the ski boat bust. This brought the number of arrested suspects in this matter to five.
- Rasheed Baderoen, Norman and Van Zyl were previously co-accused and convicted in a perlemoen smuggling case (in which a Cape Town lawyer was acquitted and, in 2019, Norman was reportedly shot at while it was unfolding).
- On 9 July, 715kg of cocaine, worth about R200-million, was intercepted at a business park in Gauteng. It had been dispatched from the Durban port. A police statement said a black Nissan bakkie, later found to belong to the state, with 23 big bags containing the cocaine was discovered and four suspects were arrested. One was a warrant officer attached to the Zonkizizwe police station in Katlehong, another was a warrant officer attached to the National Investigative Unit, the third was a chief traffic officer from Gauteng and the fourth was a civilian.
- On 30 July, 999 bricks of cocaine, worth R500-million, were discovered in a container filled with truck parts at Durban harbour. Police said investigations showed these consignments were destined for the port of Santos in Brazil.
- On 14 August, the Hawks announced a sixth ski-boat case suspect, Jaco de Kock, was arrested at a warehouse in Strand, Cape Town, identified as allegedly being used by the syndicate. Two boats, one that was being modified to have concealed compartments, were also discovered, along with the same type of bags the cocaine was discovered in, in the ski-boat bust.
- Police are still searching for three suspects in connection with the ski-boat case. Arrest warrants have been issued for two of them. One, from Israel, known by names including Ahmad Isa, Pardilov Ariel and Micky Paki, was last seen in Camps Bay, Cape Town, on 12 June when he managed to escape arrest. According to the Hawks, he is also wanted in Antwerp, Belgium, on cocaine dealing and money laundering charges and “is possibly armed ... and dangerous”.
- The second suspect is Donatas Jukna of Lithuania (New Zealand media previously reported a Lithuanian man with the same name was jailed in 2012 for two years and nine months for money laundering relating to international dealing also involving an alleged kingpin, from Lithuania, linked to drugs concealed in a Harry Potter book). Jukna was last spotted in Gauteng near the East Rand Mall on 6 June. He was meant to fly out of South Africa that day but did not. The third wanted suspect, Jonas Zulpa, is also from Lithuania.
Hawks spokesperson Lieutenant-Colonel Philani Nkwalase, referring to the R400-million ski boat bust, previously said that, aside from the work of the South African Narcotics Enforcement Bureau, the interception was made possible as a result of various actions including the FBI’s Operation Trojan Shield and the Australian Federal Police’s Operation Ironside. This shows how investigations in those countries are helping to unravel knots of global organised crime in South Africa.
Operation Trojan Shield is the codename for the project that involved the FBI secretly operating its own encrypted device company, called Anom. The Australian offshoot of this investigation was Operation Ironside.
Asked how South Africa fit into Operation Trojan Shield, another Hawks spokesperson, Katlego Mogale, told DM168: “Unfortunately that [is] operational information that cannot be divulged.”
It reportedly emerged in court this week that those arrested in the ski-boat cocaine bust were allegedly linked via FBI devices.
Criminals across the world fell for the core of this operation, Anom.
Anom – an FBI ‘front company’
An affidavit dated mid-May 2021 by Nicholas Cheviron, a special agent with the FBI, said investigators started looking into a company based in Canada, Phantom Secure, about four years ago.
They found it was selling encrypted communication devices to criminals, most of whom were drug traffickers around the world.
In March 2018, Phantom Secure’s chief executive, Vincent Ramos, was arrested and about seven months later pleaded guilty to several charges, including aiding and abetting drug distribution.
With the shutting down of Phantom Secure, FBI agents in San Francisco recruited a confidential source developing a new encrypted communication product.
“At the time, the void created by Phantom Secure’s dismantlement provided a new opportunity for criminal users to switch to a new, secure brand of device,” Cheviron said in his affidavit.
“The [source] previously distributed ... Phantom Secure ... devices to [transnational criminal organisations] and had invested a substantial amount of money into the development of a new hardened encrypted device.
“The [source] offered this next-generation device, named ‘Anom’, to the FBI to use in ongoing and new investigations.”
This was a critical move for the FBI because it meant tapping into clients who already trusted the source and, Cheviron explained, “the FBI aimed to grow the use of Anom organically through these networks”.
US’s Operation Trojan Shield
Access to Anom sparked Operation Trojan Shield. In October 2018, the source began distributing Anom devices, initially in Australia, and their popularity grew among transnational organised crime groups via word of mouth. By October 2019, Anom had several hundred users.
Cheviron said that, since October 2019, the FBI had translated “and have catalogued more than 20 million messages from a total of 11,800 devices (with about 9,000 active devices currently) located in over 90 countries”.
He said other countries started investigations “into the criminal end users of these devices”. Seventeen suspects, including from Sweden, Turkey, Serbia, the Netherlands and Australia, who allegedly distributed Anom devices and promoted the platform, have been indicted in the US.
The indictment, according to the US Department of Justice, revealed that: “The users ... openly discussed narcotics concealment methods, shipments of narcotics, money laundering, and in some groups, violent threats.”
The Anom platform was shut down on 7 June this year. However, the masses of material gleaned from messages can still be used.
Anom’s web domain appears to have been seized and says: “Law enforcement has been monitoring messages and attachments from the ANØM platform. A number of investigations have been initiated and are ongoing.”
Australia’s Operation Ironside
Three years ago, the Australian Federal Police launched an offshoot investigation from the FBI one, codenamed Operation Ironside.
This is the other police operation the Hawks said contributed to the R400-million ski boat cocaine bust in Gauteng in early June.
An Australian police statement said that, over 24 hours from 7 June, more than 224 arrests were carried out. The Australian Federal Police “also acted on 20 threats to kill, potentially saving the lives of a significant number of innocent bystanders”.
More arrests were expected to be carried out in Australia as well as other countries.
The Australian Federal Police said it was “also likely to seek extradition requests of a number of persons of interest living overseas. It comes as there have been tonnes of drugs and hundreds of arrests overseas.”
There are definite links between Australia and South Africa in terms of the drug trade.
According to a statement by Australian authorities, in January officers “in Melbourne detected an illicit substance inside a consignment of meat smokers flown into Melbourne from Cape Town, South Africa”.
The substance turned out to be methamphetamine and two suspects from that country were arrested.
In June 2019, Australian police discovered, by X-raying a second-hand excavator that arrived there from South Africa, 384kg of cocaine hidden in it.
A month earlier, in May 2019, Australian police exposed a criminal syndicate with links to Sydney Airport. “Three men [were] arrested after Australian authorities discovered illicit drugs were being transported via commercial flights from South Africa,” a statement said.
More global encryption crackdowns
Meanwhile, authorities have recently cracked down on what they believe to be other dubious globally used communication encryption services.
In March this year, the CEO of Sky Global, a company based in Canada, along with a distributor of its devices, were indicted in the US. A US Justice Department statement said: “As part of its services, Sky Global guarantees that messages stored on its devices can and will be remotely deleted by the company if the device is seized by law enforcement or otherwise compromised…
“The indictment alleges that for more than a decade, Sky Global has generated hundreds of millions of dollars in profit by facilitating the criminal activity of transnational criminal organizations and protecting these organizations from law enforcement.”
There were more than 70,000 users across the world.
In the UK, the focus was on a communication encryption service called EncroChat. According to UK court papers, a data-collecting implant in an application was placed in EncroChat devices globally and data was transmitted to French authorities (an EncroChat server was in France). Messages were collected from these devices.
In July 2020, the UK’s National Crime Agency said EncroChat’s servers were shut down and about two months earlier France and the Netherlands had managed to infiltrate it. There were about 60,000 EncroChat users worldwide. At least 746 suspects were arrested in the UK.
But the admissibility of EncroChat messages as evidence in court in the UK became a legal issue there.
In February in SA, communication surveillance was also the focus of legal proceedings. The Constitutional Court banned unregulated bulk surveillance and the State Security Agency later confirmed it was abiding by this ruling. DM168
This story first appeared in our weekly Daily Maverick 168 newspaper which is available for R25 at Pick n Pay, Exclusive Books and airport bookstores. For your nearest stockist, please click here.