The media loves a good scare story. So, apparently, do we. So when a press release from a new organisation called the Advanced Quantum Technologies Institute went out via PRNewswire on 2 March under the headline, Cybersecurity Apocalypse in 2026, the media gobbled the bait.
The press release claimed that a new algorithm – the “Jesse-Victor-Gharabaghi (JVG) Algorithm” – could crack today’s most commonly used encryption using fewer than 5,000 qubits (a measure of the capability of quantum computers), which would compress the threat timeline dramatically compared with all previous mainstream projections.
This would mean that the world economy (much of it dependent on encryption) would come crashing down before anyone had a chance to respond. Like next year or so.
Very quickly, the cryptography community responded. Hogwash, they proclaimed. Nonsense. Poppycock. They gave a slew of technical reasons why the projection was flawed and offered some choice insults directed at the PR team that released the missive.
Just like that, the panic subsided.
But the cinematic version of this scenario remains fertile. A quantum computer, humming somewhere in a government or private facility, cracks the encryption protecting the global Internet and banking system in mere minutes. Every password, every digital transaction, every classified government cable — all of it suddenly readable, exposable, exploitable. National infrastructure goes dark. Financial markets freeze. The internet, as we know it, stops being a safe place to do anything.
The threat is genuine, but…
Riveting stuff. These dystopian visions circulating with increasing frequency in tech media, security conferences and government briefings actually do have some purpose because they are not entirely wrong. The threat is genuine. Today’s dominant public-key encryption standards – RSA and elliptic curve cryptography – are theoretically vulnerable to a sufficiently powerful quantum computer running an algorithm called Shor’s algorithm.
The mathematics is settled. A machine powerful enough to execute Shor’s algorithm at scale would indeed render most of today’s encrypted internet traffic readable. Banks, hospitals, militaries, intelligence agencies, private individuals – all exposed.
But here is where the catastrophist narrative begins to strain. Because, while the media has been dramatising the threat, the world’s leading standards bodies, governments and technology companies have been quietly doing what engineers do when faced with a hard problem: solving it.
An adequate response
The response to the quantum encryption threat is already well under way, coordinated at an international level, and moving faster than most people realise.
In August 2024, the US National Institute of Standards and Technology (NIST) published the first three finalised post-quantum cryptography (PQC) standards, capping an eight-year global competition that began with 82 candidate algorithms. A fourth backup standard is expected in 2027. These are not theoretical proposals. They are the new mathematical locks designed to replace the ones that quantum computers will eventually pick.
The regulatory machinery has followed swiftly. The NSA (National Security Agency) framework requires all new US national security system acquisitions to be quantum-safe by 1 January 2027. Legacy networking equipment must be phased out by 2030. NIST will formally declare RSA and elliptic curve cryptography obsolete by 2030 and ban them entirely by 2035. A June 2025 executive order requires all federal systems to support TLS 1.3 – the protocol foundation that enables quantum-safe key exchange – by January 2030.
The United States is not acting alone. The EU published its coordinated “PQC migration roadmap” in June 2025, requiring all member states to begin the transition by the end of 2026, complete critical infrastructure migration by 2030, and finish everything by 2035. The UK has laid out a parallel three-phase plan converging on the same 2035 endpoint. Australia and Canada are on matching tracks. The international coordination here is, by historical standards, remarkably disciplined.
Advanced deployment
The practical deployment of quantum-resistant encryption is further advanced than the panic articles suggest. Cloudflare, which routes more than 20% of all global web traffic, reported in early March 2026 that more than 60% of the human-generated traffic on its network already uses post-quantum encryption via a hybrid approach — running both old and new encryption methods simultaneously, like placing two locks on every door. A year earlier, that figure was 29%. The curve is steep.
Firewall manufacturer Fortinet’s FortiOS 7.6 update includes full quantum-safe encryption for its firewall hardware.
Cisco has built dedicated cryptographic engines into its new 8000 Series Secure Routers specifically to handle PQC encryption.
Google announced a new Chrome programme in late February 2026 for making HTTPS certificates quantum-safe using a novel technique called Merkle Tree Certificate architecture, developed in collaboration with Cloudflare.
VeriSign, which operates the DNS infrastructure (the place where all global website addresses are stored) for .com and .net domains, is pioneering its own Merkle Tree approach to make quantum-safe digital signatures practical at internet scale.
But there is one real threat. It is the alarming practice already under way by adversarial states of what security researchers call “harvest now, decrypt later” — the bulk collection of currently encrypted data and files, stored quietly in anticipation of future quantum decryption capability. Those files will be under “old” lock and key, protected from re-encryption by newer quantum-resistant wizardry.
There is no real technical solution to this, but there are some attempts to figure out where currently encrypted files live within organisations. A US Office of Management and Budget mandate now requires every federal agency to submit an annual inventory of systems using vulnerable encryption until the end of 2035. NIST’s National Cybersecurity Center of Excellence has an entire workstream dedicated to cryptographic discovery.
SandboxAQ, a company spun out of Alphabet, secured a five-year contract with the Department of Defence in December 2025 to deploy automated cryptographic scanning across Pentagon systems. The boring but essential work of finding and cataloguing every vulnerable lock is already under way.
But here’s the thing about catastrophist narratives in technology: they have a poor track record (I know, I know, maybe this time is different).
Echoes of Y2K
The most instructive parallel is Y2K. In the years leading up to 31 December 1999, media coverage of the Millennium Bug was saturated with apocalyptic predictions – planes falling from the sky, nuclear power plants going haywire, ATMs dispensing nothing, the global financial system grinding to a halt. The threat, to be clear, was real. Two-digit year fields in legacy software really were a genuine problem. But the world invested heavily in fixing it, engineers did their jobs, and nothing much happened.
The quantum encryption problem rhymes closely with Y2K. The threat is real. The technical challenge is significant. The scale is large. But the engineering community has already identified the problem, developed the solutions, established the standards, set binding regulatory timelines and begun deploying fixes at scale. Governments on multiple continents are spending serious money on it. The world’s largest internet infrastructure companies have made it a product priority.
Realistic assessment
The timeline also matters. No quantum computer today is anywhere near the scale required to break RSA-2048 encryption. Current estimates from serious researchers – not the alarmist variety – suggest that a cryptographically relevant quantum computer is probably a decade or more away. The 2035 deadline set by NIST and mirrored by the EU and UK is not arbitrary. It reflects a realistic assessment of how long it will take for quantum hardware to become genuinely threatening, and how long it will take to complete an internet-scale migration.
The challenges are real and not trivial. The new quantum-safe signature algorithms produce keys and certificates dramatically larger than the old ones. This creates genuine performance and bandwidth challenges, particularly for the digital certificate layer of internet security.
These problems are being actively worked on, with companies such as Google and VeriSign developing architectural innovations to manage the size issue without degrading performance.
Messy, but not apocalyptic
None of this is comfortable. It is expensive, complex and slow. Legacy systems take years to upgrade. Third-party software dependencies are a nightmare to audit. International supply chains introduce risks that no single government can fully control. The migration, in practical terms, will be messy and uneven. Some organisations will be late. Some will be caught out.
But “messy and uneven” is a long way from “civilisational collapse.” The encryption apocalypse scenarios flooding tech media share a common flaw: they assume the threat is moving and the defence is standing still. The reality is closer to the opposite. A sufficiently powerful quantum computer does not yet exist. The post-quantum cryptography standards do. The regulatory mandates do. The deployment is already happening, at scale, on the networks that move the majority of global internet traffic.
The quantum threat to encryption is real. The engineering response to that threat is also real. What is not real is the implicit assumption underlying most of the alarm – that the world will be caught flat-footed when “Q-Day” arrives. The people whose job it is to prevent that outcome are already on the job, and they are well ahead of schedule.
I like to think that we can sleep reasonably well.
For a deep dive into the companies building the quantum protection ecosystems, read this post from Chris Wood.) DM
Steven Boykey Sidley is a professor of practice at JBS, University of Johannesburg, a partner at Bridge Capital and a columnist-at-large at Daily Maverick. His new book, It’s Mine: How the Crypto Industry is Redefining Ownership, is published by Maverick451 in SA and Legend Times Group in the UK/EU, available now.





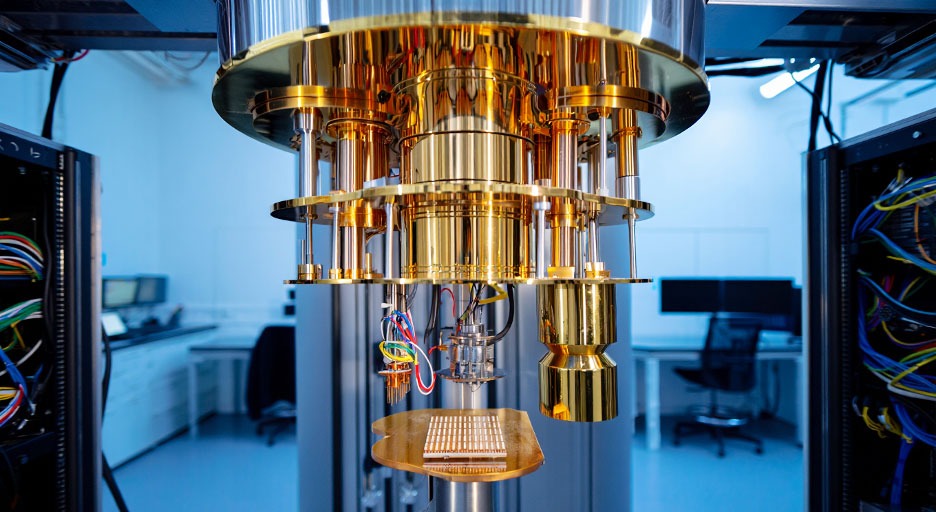 The quantum threat to encryption is real, but the people whose job it is to prevent a chaotic outcome are already on the job, and they are well ahead of schedule. (Image: reve.art)
The quantum threat to encryption is real, but the people whose job it is to prevent a chaotic outcome are already on the job, and they are well ahead of schedule. (Image: reve.art)