Fraudsters across the globe are preying on people left desperate by the Covid-19 pandemic. In South Africa, in recent months scammers have masqueraded as the Public Investment Corporation (PIC), the South African Revenue Service (SARS), Transnet and provincial and national health departments.
The PIC had to warn people not to respond to SMSs supposedly qualifying recipients for a fake PIC-sponsored “Business Personal Relief Fund”. According to the PIC, if a person responds to the email address supplied, info@thepub.co.za, they receive an “approval” letter and will have to pay a “handling fee” before the promised relief funds are deposited.
“The PIC is not sponsoring the alleged Covid-19 Business Personal Relief Fund and is of the view that this is an attempt by cunning and ruthless fraudsters whose ultimate goal is to take advantage of vulnerable people when the country is grappling with the coronavirus pandemic,” it said in a statement.
Deon Botha, PIC’s head of corporate affairs, told amaBhungane that the state-owned investment manager was notified of the scam on 5 May.
“So far, we have had two people report the scam, with one having responded to the scam. It was necessary for the PIC to act swiftly to ensure that people do not fall prey to fraudulent activities that perpetuate the PIC’s name and brand,” Botha said.
“This is the first scam of this nature we have been made aware of,” he said, adding that the PIC had alerted law enforcement agencies.
Last month, amaBhungane reported how scammers targeted businesses listed on the national Treasury’s central supplier database — a scam tailor-made for the coronavirus pandemic.
The fraudulent messages, SARS said, were “aimed at enticing unsuspecting taxpayers to part with personal information such as bank account details”.
The PIC scam appears to be a resuscitation of earlier cons.
A domain name search shows that scammers using the free web address “thepub.co.za” have targeted job seekers via several fax scams.
JobMail warned of the fax scams in 2011 when a recruiter asked a person to fax their CV: “This fax number is set up to incur charges beyond standard rates. So, if you send your CV to this ‘fake recruiter’, you will be charged on your telephone bill at a very high rate.”
These documents, as one person explained, could end up being over 20 pages long. The result? An expensive fax bill and a scammer with access to your detailed personal information.
One of the few remaining ads that contain an advert from the job scam email, perfectjobs@thepub.co.za, is a 2014 advert advertising a position for a telemarketer with two years’ experience. This email address was later added to three lists in 2015, 2016 and 2017 of emails connected to job fax scams.
… and SARS
Since the start of the year, SARS has warned South Africans against responding to “spoofed” emails and SMSs regarding tax returns, audit queries and missing income tax documents from domain names similar to the official SARS name, sars.gov.za.
The fraudulent messages, SARS said, were “aimed at enticing unsuspecting taxpayers to part with personal information such as bank account details”.
“For the period starting from 1 March 2020, there were 23 confirmed phishing attacks reported to SARS. All the fraudulent websites have since been taken down,” said SARS head of communication Siphithi Sibeko.
He added that SARS had received more than 400 emails reporting phishing attacks from taxpayers since 1 March.
“The SARS anti-phishing team ensures that fraudulent websites are taken down and fake sender email addresses are reported to the relevant ISPs [internet service providers]. Tracking the fraudsters is almost impossible. Fraudsters make use of compromised websites, fake email addresses, compromised email servers as well as anonymity networks to effectively hide their true identity,” revealed Sibeko.
Many of the scams are sophisticated and look legitimate. A business owner who fell for the industrial sanitiser machine scam that amaBhungane reported on last month provided us with details of how he was nearly swindled out of R405,000.
The business owner told amaBhungane that everything had seemed legitimate. “They even had the stamp on the documents.”
He has since opened a criminal case with the police.
The bank which the scammers used for this fraud has frozen two connected accounts.
… and Transnet
A Transnet scam is also doing the rounds.
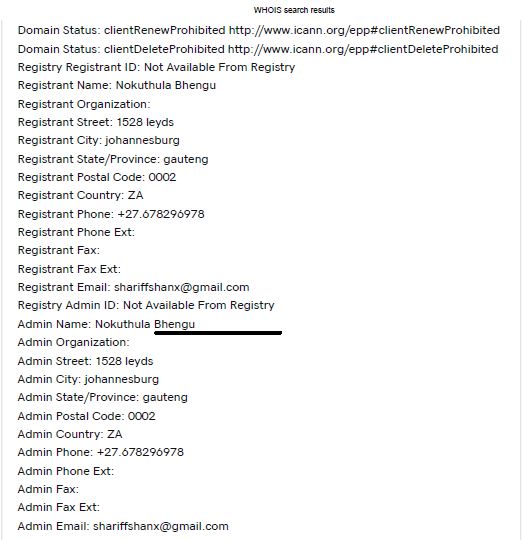
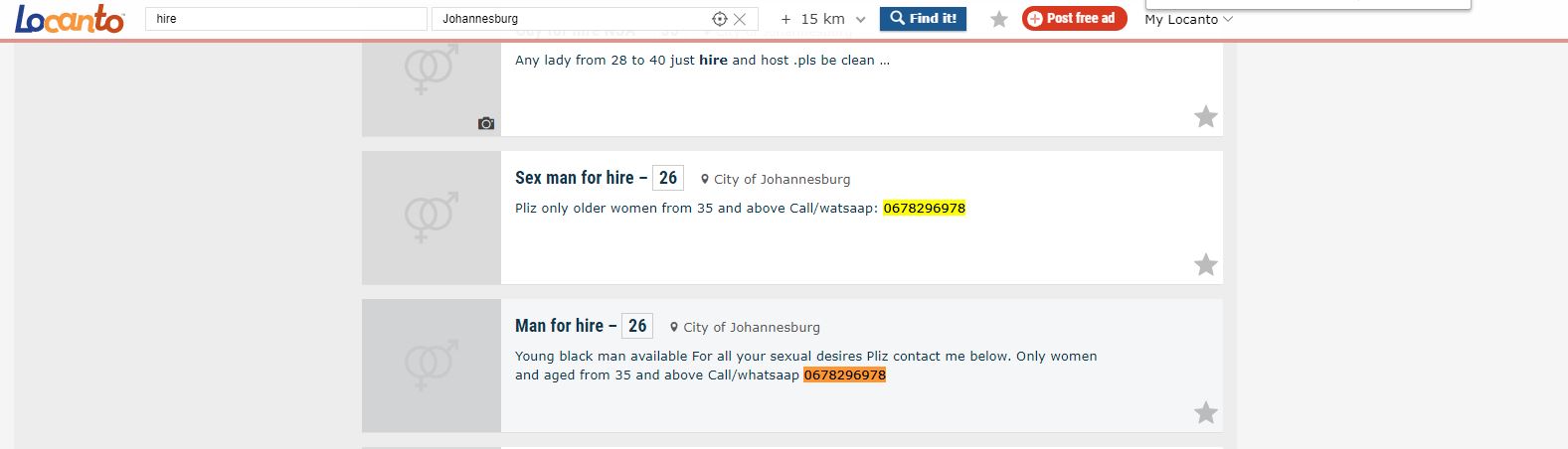
On 2 January 2020 at 14:36, someone bought the domain name Transnetengineerings.net, which is very similar to the legitimate website of Transnet’s engineering division, Transnetengineering.net, the only difference being the additional “s”. 
In April, “Transnet” requested proposals for the supply of 31 Kerfax e400 hospital beds via the transnetengineerings.net domain. The document mimicked legitimate tender documents, down to the name of staff members in the procurement office.
AmaBhungane contacted one of these staff members, who confirmed the e400 Hospital bed request was a scam.
We contacted the landline number on the fake request for quotation document and a “Transnet official” answered the call. When we asked why Transnet needed hospital beds, the operator told us they would be donated to the state-of-the-art Steve Biko Academic Hospital in Tshwane.
AmaBhungane got hold of the hospital’s procurement staff, who rubbished the idea that Transnet would provide the facility with more beds. The hospital currently has over 800 beds, plus 53 ICU beds, 21 high-care beds, 61 observation beds and 108 beds in the oncology complex.
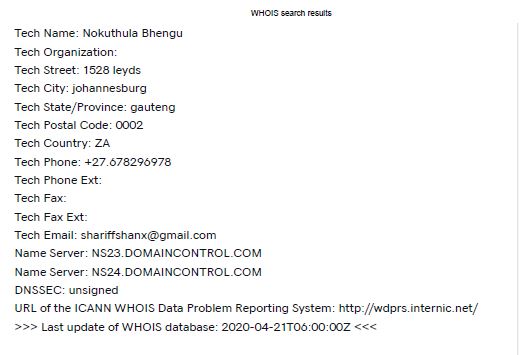
And the owner of the website? The only trace we could find was a March 2020 classified ad for sex work. DM
In Addition: Uptick in scammers and malware – report
International cybersecurity company Mimecast monitored the first 100 days of lockdown and found a global increase in “coronavirus-related spam and impersonation attack campaigns” preying on the vulnerability of people at home and “taking advantage of their desire for information about the coronavirus pandemic to entice them to click on unsafe links”.
“Traditional fraudsters are also using spam to offer fake or non-existent goods such as protective masks or Covid-19 cures,” the report noted.
Mimecast said it detected a 26% increase of opportunistic scams, a 30% increase in impersonations, 35% in malware and 55.8% in blocked URLs and malicious software from January 2020 to the end of March.
Towards the end of March, Mimecast had blocked the delivery of over 83 million Covid-19-related emails as spam/opportunistic since January.
One case involved an impersonation of the US Centres for Disease Control and Prevention, with the scammer trying to get members of the public to click on links that revealed coronavirus cases in their area.
Other scams tried to persuade users to reveal personal logins for working platforms such as Microsoft’s One Drive.
The report’s authors said they believed attacks would continue throughout the crisis, targeting people’s fears as they were furloughed from work and their cash flows dried up.
The next round of malicious campaigns is likely to take the form of organisations promising to help travellers recoup expenses from cancelled trips or, as with the PIC scam, connecting people to a government grant.
Advocate Jacqueline Fick, a local expert in electronic fraud, asked people to err on the side of caution: “Phishing emails are set up to deceive the recipient and convince you to divulge information or to get you to act on the request in some other form. In these tough economic times, it becomes even more tempting to respond to such requests. At the best of times it can be difficult to distinguish between a fake and legitimate email.” DM
Previously this article mentioned several scams connected to therugby.co.za regarding its shared IP address with thepub.co.za. While info@thpub.co.za and perfectjobs@thepub.co.za have been positively linked to the scams mentioned in this article, the author has since learnt that both therugby.co.za and thepub.co.za are also free web email addresses, like Gmail and Yahoo, which may have many other innocent users. The author has since reached out to Webmail to see if they are willing to identify people behind those specific addresses, and others that may be linked to on the webmail platform.
The amaBhungane Centre for Investigative Journalism, an independent non-profit, produced this story. Like it? Be an amaB Supporter to help us do more. Sign up for our newsletter to get more.




![malware 02 [Converted]](https://cdn.dailymaverick.co.za/dailymaverick/wp-content/uploads/amab-covid19Scams.jpg) (Photo: Adobestock)
(Photo: Adobestock)